CLOUD & VIRTUALIZATION MANAGED SERVICES
- CLOUD & VIRTUALIZATION STRATEGY: defining the best hardware, software and Cloud Providers for the company.
- CLOUD & VIRTUALIZATION DESIGN: AdvisionIT offers VMware, Microsoft Hyper-V and Open source virtualization platforms based on the client needs and budget for on-premise implementation. The Cloud options are AWS, Azure, Google and some private and boutique Cloud Providers like CloudSigma.
- CLOUD & VIRTUALIZATION MANAGEMENT: Capacity, performance and on-going maintenance.

Named Account Manager
for any business and Project related questions

Cloud Engineers & Virtualization Specialists
available 24/7/365

Named Service Manager
for any technical questions

Professional Services

Architecture advisors

Managed Monitoring and Incident Response

Cloud & Virtualization experience

Security advisors
If you are asking yourself why:
- Your business has a full cabinet of servers and network equipment which are not utilized well.
- Every time you need to add another service you are in position to add more hardware and that is the only option for you.
- Your systems are constantly consuming power that increases your monthly payments to the Data Centre and heating up the Rack.
You can contact us to advise and guide you how to create a fully redundant and highly available hybrid setup - Cloud&On premise system that can scale up in the future. That will definitely lower your maintenance costs while providing you with the necessary redundancy and scalability.
These are just samples of the Cloud&Virtualization managed services we can provide. Please contact us for more information, or to discuss additional service needs that are not on this list.
⇒ Advanced Vision IT Ltd Technology Stack & Products
Managed technology stack refers to a set of IT tools and services that are outsourced to the Advanced Vision IT team for management and maintenance. This typically includes hardware, software, network infrastructure, applications, and data storage. If you want to view some of the ADVANCED VISION IT's managed technology stack solutions, click on the links below.
- Linux managed services refer to outsourced IT services that provide ongoing management and support for Linux-based systems.
- Microsoft Managed Services refer to a range of services that are provided by Microsoft or Microsoft partners to help organizations manage and maintain their IT infrastructure and services. These services are designed to help organizations improve their IT performance and reduce the cost and complexity of managing their IT systems.
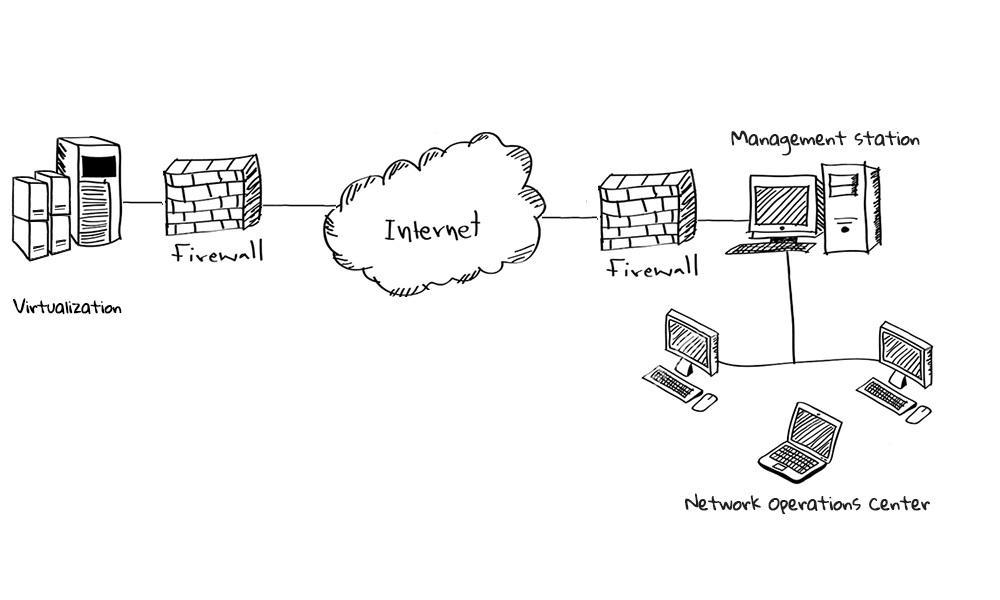
- Network managed services refer to outsourcing management and maintenance of an organization's network infrastructure to a third-party service provider. This includes services such as monitoring, maintenance, troubleshooting, configuration, and optimization of network devices such as routers, switches, firewalls, and wireless access points.
- Database managed services refer to outsourcing the management and maintenance of databases to a third-party provider. With database-managed services, the provider takes care of the day-to-day operation and maintenance of databases, including tasks such as backups, patches, upgrades, monitoring, and performance tuning.
- Cloud backup and storage managed services are services that provide organizations with the ability to back up and store their data in the cloud while also providing management and monitoring of the backup and storage infrastructure.
⇒ Advanced Vision IT Ltd Cybersecurity Products & Software
To build good cybersecurity protection, you need physical products and software that will help strengthen your network against attacks. If you want to view some of the ADVANCED VISION IT's cyber protection solutions, click on the links below.
- Endpoint security and antivirus software - offer a centralized management system from which security administrators can monitor, protect, and investigate vulnerabilities across all endpoints, including computers, mobile devices, servers, and connected devices. Antivirus software helps keep a computer system healthy and free of viruses and other types of malware.
- Employee Monitoring Solution - Employee monitoring solutions are software tools that enable employers to monitor the activities of their employees while they are at work. These solutions can be used to track employees' computer usage, including their internet browsing history, email communication, keystrokes, and application usage.
- Cybersecurity Backup - A backup is a copy of the system or network's data for file restoration or archival purposes. Backups are an essential part of a continuity of operations plan as they allow for data protection and recovery.
- Еmail Protection - refers to technology designed to prevent, detect and respond to cyber-attacks delivered through email. The term covers everything from gateways email systems to user behavior to related support services and security tools.
- Password Vault Manager - A password vault, password manager, or password locker is a program that stores usernames and passwords for multiple applications securely and in an encrypted format. Users can access the vault via a single “master” password.
- Vulnerability Assessment & Patch Management - The main difference between patch management and vulnerability management is that patch management is the operational process of applying remediations (patches) to vulnerable systems. Vulnerability management is the process of identifying, scanning, and prioritizing vulnerabilities for remediation.
- Data loss prevention (DLP) - makes sure that users do not send sensitive or critical information outside the corporate network.
- Cloud Security- Cloud security is a collection of security measures designed to protect cloud-based infrastructure, applications, and data. These measures ensure user and device authentication, data and resource access control, and data privacy protection.
- Next-Generation Firewall - protects your network by filtering traffic and acting as a guard between your internal network and the rest of the world. Without a Firewall, your business systems could be left wide open and vulnerable to attack. It also serves as another protective layer to block malicious software.
- Active Directory Security and Recovery are critical components of any organization's cybersecurity strategy. Here are some key steps that can be taken to secure and recover Active Directory.
- SIEM & SOAR - SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are both tools used in cybersecurity to monitor and respond to security threats.













